 Versie 5.0.1 van WordPress is uitgekomen. Met dit programma, dat onder een gpl beschikbaar wordt gesteld, is het mogelijk om een website of blog op te zetten en bij te houden. WordPress is eenvoudig in te stellen en kan binnen vijf minuten draaien mits er al een server met php en MySQL beschikbaar is. Er zijn mogelijkheden om de functionaliteit van WordPress verder uit te breiden met plug-ins en het uiterlijk met thema's aan te passen.
Versie 5.0.1 van WordPress is uitgekomen. Met dit programma, dat onder een gpl beschikbaar wordt gesteld, is het mogelijk om een website of blog op te zetten en bij te houden. WordPress is eenvoudig in te stellen en kan binnen vijf minuten draaien mits er al een server met php en MySQL beschikbaar is. Er zijn mogelijkheden om de functionaliteit van WordPress verder uit te breiden met plug-ins en het uiterlijk met thema's aan te passen.
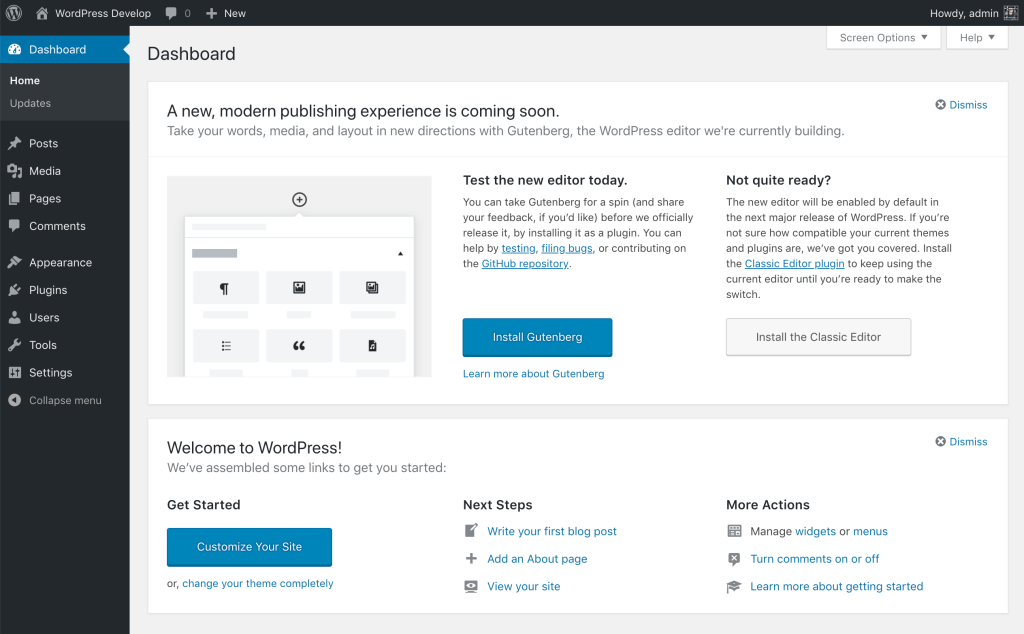
Versie 5.0 bevat onder meer een compleet vernieuwde editor en een nieuw standaard thema. De oude editor is ook nog steeds aanwezig en draagt nu de naam classic editor. De release notes voor deze uitgave kunnen hieronder worden gevonden. In deze update zijn diverse beveiligingsproblemen verholpen.
WordPress 5.0.1 Security ReleaseWordPress 5.0.1 is now available. This is a security release for all versions since WordPress 3.7. We strongly encourage you to update your sites immediately.
Plugin authors are encouraged to read the 5.0.1 developer notes for information on backwards-compatibility.
WordPress versions 5.0 and earlier are affected by the following bugs, which are fixed in version 5.0.1. Updated versions of WordPress 4.9 and older releases are also available, for users who have not yet updated to 5.0.
- Karim El Ouerghemmi discovered that authors could alter meta data to delete files that they weren’t authorized to.
- Simon Scannell of RIPS Technologies discovered that authors could create posts of unauthorized post types with specially crafted input.
- Sam Thomas discovered that contributors could craft meta data in a way that resulted in PHP object injection.
- Tim Coen discovered that contributors could edit new comments from higher-privileged users, potentially leading to a cross-site scripting vulnerability.
- Tim Coen also discovered that specially crafted URL inputs could lead to a cross-site scripting vulnerability in some circumstances. WordPress itself was not affected, but plugins could be in some situations.
- Team Yoast discovered that the user activation screen could be indexed by search engines in some uncommon configurations, leading to exposure of email addresses, and in some rare cases, default generated passwords.
- Tim Coen and Slavco discovered that authors on Apache-hosted sites could upload specifically crafted files that bypass MIME verification, leading to a cross-site scripting vulnerability.

:strip_exif()/i/2002139227.png?f=thumbmedium)