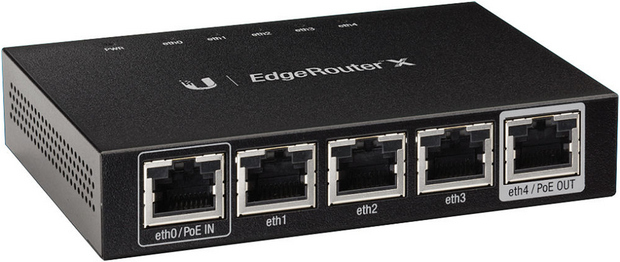
 Ubiquiti heeft versie 1.8.5 uitgebracht van EdgeMax, de beheersoftware die op verschillende EdgeRouters van het bedrijf draait. De EdgeRouters kenmerken zich door uitgebreide instelmogelijkheden, maar vergen wel enige netwerkkennis om het goed draaiende te krijgen. Ook zijn lang niet alle instellingen via de gui aan te passen en zul je dus via de command line aan de gang moeten. Hieronder is de lijst met veranderingen en verbeteringen te vinden die sinds versie 1.8.0 zijn aangebracht.
Ubiquiti heeft versie 1.8.5 uitgebracht van EdgeMax, de beheersoftware die op verschillende EdgeRouters van het bedrijf draait. De EdgeRouters kenmerken zich door uitgebreide instelmogelijkheden, maar vergen wel enige netwerkkennis om het goed draaiende te krijgen. Ook zijn lang niet alle instellingen via de gui aan te passen en zul je dus via de command line aan de gang moeten. Hieronder is de lijst met veranderingen en verbeteringen te vinden die sinds versie 1.8.0 zijn aangebracht.
New features
Enhancements and bug fixes
- [Offload] Add "Hardware NAT" offload function for the ER-X platform (i.e., ER-X, ER-X-SFP, and EP-R6 models), which can significantly improve packet forwarding performance while reducing CPU utilization. Currently this supports IPv4 and IPv6 traffic including VLAN, PPPoE, bridging, etc. Currently this is disabled by default and can be enabled by:
set system offload hwnat enable- [Switch] Add "per-port VLAN" feature for the ER-X platform. Now "untagged" and "tagged" VLANs can be set for each port in "switch mode" on the ER-X platform (including ER-X, ER-X-SFP, and EP-R6). This can be configured using configuration dialog for switch0 in the Web UI. Or using the CLI, for example:
set interfaces switch switch0 switch-port vlan-aware enable set interfaces switch switch0 switch-port interface eth3 vlan pvid 100 set interfaces switch switch0 switch-port interface eth3 vlan vid 200 set interfaces switch switch0 switch-port interface eth3 vlan vid 300This would set VLAN 100 to be "untagged" on port eth3, and VLANs 200 and 300 are "tagged" on port eth3. Note that the global "vlan-aware" setting (default disabled) enables the new "per-port VLAN" feature. If this is not enabled the swith ports will function the same way as before, i.e., simple L2 switching with no per-port VLAN and will pass all VLANs automatically. Also none of the per-port VLAN settings will have any effect if vlan-aware is not enabled.- [DPI/Traffic Analysis] Add DPI and Traffic Analysis features for the ER-X platform (including ER-X, ER-X-SFP, and EP-R6 models). This means all current models now have support for DPI/Traffic Analysis. The features function as with the other platforms, and it is disabled by default as well and can be enabled from the Web UI Traffic Analysis page or using the CLI:
set system traffic-analysis export enable set system traffic-analysis dpi enableA few things to note:
- If the new "HW NAT" offload feature for ER-X is also enabled, traffic to which HW NAT is applied is handled by the hardware directly and therefore Traffic Analysis/DPI cannot see such traffic.
- Also, similar to the offload features for the older platforms, certain traffic is not eligible for offload, e.g., traffic that requires QoS policy cannot be offloaded.
- This means that on the ER-X platform when both Traffic Analysis/DPI and HW NAT offload are enabled, it is possible for some traffic to be seen in Traffic Analysis/DPI but not others, e.g., traffic requiring QoS cannot be offloaded and therefore can be seen by Traffic Analysis/DPI.
Fixes/changes for issues found/reported during alpha/beta testing:
- [IPsec] Change implementation of "initiate" connection type as the original implementation does not work well with the newer version of strongSwan. More specifically, it now uses "auto=route" instead of "auto=start" (which is not recommended by strongSwan as it could be broken in cases).
- [IPsec] Change the VTI interface handling logic so that the link up/down is no longer tied to the IPsec status. (Note that this is not the same as changing the script to not "down" the interface which was discussed previously, since that would still tie the link "up" to the IPsec status.)
- [IPsec] Make "ipsec-interfaces" setting deprecated (it is not actually used for the strongSwan config and also causes warning with the new version of strongSwan).
- [IPsec] Add validation for aggressive mode to disallow its use with PSK (since it is not allowed by strongSwan by default).
- [IPsec] Add validation for RSA authentication to disallow its use if peer is 0.0.0.0 (any).
- [IPsec] Add more crypto options for ESP group configuration, including "aes128gcm128" and "aes256gcm128" for "encryption" and "sha256", "sha384", and "sha512" for "hash".
- [IPsec] Fix packaging for strongSwan packages to include the "pki" tool.
- [IPsec] Change log level for IPsec offload log messages that are not useful in most cases.
- [Offload] Fix possible "download corruption" issue triggered by packet corruption that happened upstream (before reaching the router). There have been several reported cases over the years that were possibly caused by this issue.
- [DNS forwarding] Update the underlying dnsmasq software to the current version 2.75, now building/packaging it ourselves. The new version includes quite a few new features, which are not yet explicitly supported in the router configuration but can be used with the free-form "options" config setting for DNS forwarding for example.
- [System] Update iproute2 to version 4.4.0 for enhancements/fixes (e.g., ip6gre tunnel, possible fix for segfault, etc.).
- [System] Change upgrade code to delete old version first if if there is not enough space for the upgrade operation. For CLI upgrade this will ask the user for confirmation, and it's automatic when doing upgrade through the Web UI. In particular, this is useful for the ER-X platform which has more limited storage and may often require it. (Of course the new upgrade code will only take effect at the next upgrade.)
- [System] Only load MPLS forwarding module when MPLS-related features are configured. This avoids the performance overhead from the module when MPLS is not configured.
- [System] Update copyright date in Web UI and CLI.
- [System] Adjust sudo logging level to avoid spamming syslog with successful messages at default syslog level.
- [System] Apply appropriate permissions and cleanup to temporary file created by commit-revisions feature.
- [System] Fix long boot time in some cases when DNS server is not reachable, which may also cause other config issues.
- [System] Add support for new SSH key types for user public key and the "loadkey" command.
- [System] Fix local IP address check for IPv6 addresses.
- [System] Fix typo in the "vyatta-bridge.pl" script.
- [Web UI] Update to PHP version 7 with the required cross-build changes and fixes.
- [Web UI] Remove support for legacy browsers, and "native WebSocket" support is now required, for example the following browsers are supported:
Note that since the "legacy support" was using Flash to support WebSocket on older browsers, this means the Web UI is now 100% "Flash-free". Also this means the removal of the "vfpolicyd" daemon which was listening on port 843 to support the Flash fallback for WebSocket.
- Any recent versions of FireFox
- Any recent versions of Chrome
- IE 10 or higher
- Edge
- Safari 7 or higher
- [Web UI] Add support for using only newer (stronger) ciphers for HTTPS. Note that older ciphers are required for wider browser compatibility, but if that is not a concern, they can be disabled by
set service gui older-ciphers disableIf older ciphers are disabled, the ones used are (based on Mozilla "Modern" recommendations):ECDHE-ECDSA-AES256-GCM-SHA384 TLSv1.2 Kx=ECDH Au=ECDSA Enc=AESGCM(256) Mac=AEAD ECDHE-RSA-AES256-GCM-SHA384 TLSv1.2 Kx=ECDH Au=RSA Enc=AESGCM(256) Mac=AEAD ECDHE-ECDSA-AES128-GCM-SHA256 TLSv1.2 Kx=ECDH Au=ECDSA Enc=AESGCM(128) Mac=AEAD ECDHE-RSA-AES128-GCM-SHA256 TLSv1.2 Kx=ECDH Au=RSA Enc=AESGCM(128) Mac=AEAD ECDHE-ECDSA-AES256-SHA384 TLSv1.2 Kx=ECDH Au=ECDSA Enc=AES(256) Mac=SHA384 ECDHE-RSA-AES256-SHA384 TLSv1.2 Kx=ECDH Au=RSA Enc=AES(256) Mac=SHA384 ECDHE-ECDSA-AES128-SHA256 TLSv1.2 Kx=ECDH Au=ECDSA Enc=AES(128) Mac=SHA256 ECDHE-RSA-AES128-SHA256 TLSv1.2 Kx=ECDH Au=RSA Enc=AES(128) Mac=SHA256- [Web UI] Add new config setting for the "HTTP port" of the Web server, for example:
set service gui http-port 8080The HTTP port now also observe the configured "listen-address" as well (previously it always listens on all interfaces).- [Web UI] Implement proper HTTP-to-HTTPS redirect in the case of non-default HTTP and HTTPS ports. Previously the code always used port 443 for HTTPS and therefore the redirect breaks if non-default HTTPS port is used.
- [Web UI] Add new config settings for Web server certificate files. For example, to specify a particular server certificate (including private key):
set service gui cert-file /config/auth/server.pemTo specify a "CA file" for chained certificates:set service gui ca-file /config/auth/ca.pem- [Web UI] Fix sorting issue on the Traffic Analysis page for entries with "Tbytes" unit. [Web UI] Add the "VPN Status" feature wizard.
- [Web UI] Add the "DNS host names" feature wizard.
- [Web UI] Add burst rate and burst size settings to Advanced Queue leaf node config
- [Web UI] Fix issue with Traffic Analysis page caused by config changes under System.
- [Web UI] Fix Smart Queue config issue where changes are not saved when Smart Queue is deleted.
- [Web UI] Fix issue where some dynamic IPv6 addresses are not displayed on the dashboard.
- [Web UI] Use SHA256 when generating certificate for the Web server.
- [Web UI] Add support for more than two WAN interfaces in the load balancing wizard. Also change the wizard to allow more flexible selection for the WAN/LAN interfaces.
- [Web UI] Fix IPv6 address handling when upper case characters are used in the config.
- [Web UI] Fix validations for hostname in the DNS hostname wizard.
- [Web UI] After login, ask user whether basic setup wizard is needed if the router is running with default config.
- [Web UI] Fix help text typos.
- [Web UI] Enable "authoritative" setting for DHCP server config set up by the setup wizards.
- [Web UI] Fix packaging issue for the "load balancing2" setup wizard for the ER-X platform.
- [Web UI] Fix counters display of switch ports for the ER-X platform.
- [Web UI] Fix duplicate display of IPv6 address containing leading zeros.
- [Web UI] Fix firewall rule number display when reordering rules but not saving.
- [Web UI] Update validation for host name to be consistent with the CLI configuration.
- [Web UI] Fix firewal rule validation for protocol.
- [Web UI] Add support for TCP reject action for firewall rules
- [Web UI] Change firewall rule reordering so that rule numbers are incremented by 10 (i.e., 10, 20, 30, ...) after reordering.
- [Web UI] Fix branch node creation for Advanced Queue.
- [Traffic Analysis] Improve handling of "external IPs" to reduce less useful entries occupying Traffic Analysis data (however this may not eliminate all cases of "external IP" entries).
- [Traffic Analysis/DPI] Improve handling of flow stats in some cases.
- [DPI] Add built-in categories including "Web".
- [DPI] Add validation to disallow DPI application matching in firewall and advanced queue on platforms that do not support DPI yet.
- [DPI] Fix firewall rule configuration when Instant-Messaging category is specified.
- [DPI] Modify signature update script to only extract specific files.
- [DPI] Add configuration for hour of day (local time) to check update for new DPI signatures, e.g.:
set system traffic-analysis signature-update update-hour 3would check for updates between 3 AM and 4 AM. Or to disable signature update:set system traffic-analysis signature-update disable- [Interface] Enable Ethernet flow control (pause frames) auto-negotiation by default on all interfaces of all models (except the "combo" ports on the ER Pro). Note that it still requires auto-negotiation and so pause frames will only be used if the other side also supports and advertises pause frames.
- [Interface] Fix kernel setting for eth5 (SFP port) on the ER-X-SFP and EP-R6.
- [Interface] Fix some auto-negotiation/speed issues for the SFP port on ER-X-SFP.
- [Interface] Fix interface route handling when interface has no address.
- [Interface] Disallow deleting physical interfaces to prevent issues with config out-of-sync with system.
- [Interface] Fix timing issue with dynamic interface handling when a dynamic interface is created while a commit is ongoing.
- [Interface] Add "proxy-arp-pvlan" setting for interfaces.
- [Interface] Add support for setting MAC address on VLAN interface.
- [BGP] Fix attribute flag validation to handle extended length correctly.
- [BGP] Fix "as-path-prepend" config with single AS specified.
- [BGP] Fix possible memory corruption that was causing the routing daemon to crash in some cases.
- [BGP] Lower log level for "Withdraw: Can't find route" messages that are not normally useful.
- [BGP] Fix handling of confederation ID and peer to allow extended ASN.
- [BGP] Remove deprecated config setting including disable-network-import-check.
- [BGP] Add "show bgp l2vpn" commands for VPLS/BGP status:
show bgp l2vpn show bgp l2vpn detail- [BGP] Fix handling of nexthop interface flapping to ensure BGP route getting inserted into kernel table.
- [BGP] Fix BGP route-map community config to allow community value 0.
- [BGP] Fix "bestpath as-path confed" configuration setting.
- [BGP] Fix BGP daemon crashing due to issue with parsing extended community message.
- [BGP] Fix configuration ordering and other issues related to "update-source" setting.
- [BGP] Fix BGP daemon crashing due to issue with parsing graceful-restart capabilities.
- [Routing] Fix incorrect recursive route handling causing ribd to use 100% CPU.
- [Routing] Fix "martian" address detection in routing code.
- [RIP] Fix MD5 authentication config.
- [SNMP] Fix SNMP support for routing protocol daemons.
- [SNMP] Improve error message for listen-address configuration with IPv6 link-local address but no interface.
- [SNMP] Fix possible SNMP startup issue with SNMPv3 configuration.
- [Advanced Queue] Allow "ip", "ether", "mark", and "application" match criteria to be specified in the same filter to provide more flexibility.
- [Smart Queue] Fix config issues and add validations to prevent invalid config (e.g., neither upload nor download is configured).
- [PPPoE client] Fix interface rename when IPv6 is configured on the PPPoE interface.
- [QoS] Remove the "set-dscp" setting from traffic-policy as it does not work "correctly" and causes issues. In most cases, setting DSCP can already be done using "firewall modify" rules instead (which also allows more flexible matching criteria etc.).
- [Dynamic DNS] Add No-IP service as an explicit option for DDNS configuration both in CLI and Web UI.
- [L2TP/IPsec] Update config validation so that it no longer requires deprecated IPsec settings (interface and NAT traversal settings).
- [PPTP server] Fix typo in config help text.
- [MPLS] Change "propagate-ttl" to disabled by default, which is consistent with the default config. Note that this only partially fixes the. More specifically, enabling "propagate-ttl" still has no effect and we will need to fix that.
- [OSPFv3] Reorganize OSPFv3 config settings by moving most settings under "parameters" up one level (to be more consistent with original OSPF config structure).
- [OSPFv3] Fix "passive-interface default" setting and add "passive-interface-exclude" setting.
- [IGMP proxy] Apply patch for IGMPv3 support.
- [Kernel] Enable CONFIG_XFRM_STATISTICS in kernel config to provide more stats/information for IPsec troubleshooting.
- [CLI] Fix SNMP config to eliminate Perl error when configuring SNMPv3 without privacy.
- [CLI] Fix help text for SNMP "listen-address" and "network" to make it clear IPv6 address/network is supported.
- [CLI] Fix handling of user password starting with the '-' character.
- [CLI] Remove obsolete "show disk" commands.
- [Firewall] Fix issue with time-based firewall rule using incorrect time after daylight saving time change.
Updated software components
- [Offload] Fixes for the "HW NAT" offload feature on ER-X platform (including ER-X, ER-X-SFP, and EP-R6):
These fixes/enhancements should address the issues in v1.8.5alpha1
- Fix "hwnat" configuration for "non-root" user on ER-X platform.
- Fix the issue where offload does not work if ISC DHCP server (and possibly other software) is running
- Fix certain corner cases when offload is in effect that could cause the switch to stop functioning
- [Offload] Fix switch issue on ER-X platform where the switch stops working when encountering certain IPTV traffic with "HW NAT offload" enabled.
- [Offload] Fix packet counters for ethX interfaces when HW NAT offload is enabled on ER-X platform.
- [Offload] Fix IPv6 HWNAT offload on ER-X platform when IPv6 firewall rules are configured.
- [IPsec] Fix "restart vpn" command which was checking deprecated config settings.
- [DNS forwarding] Fix dnsmasq crash issue.
- [Web UI] Change default for "older-ciphers" to "enable". This allows users with older browsers to continue accessing the Web UI after upgrade. It can be set to disable if browser compatibility is not a concern.
- [Web UI] Fix switched ports not being displayed in the switch0 config dialog.
- [Routing] Change routing daemons to only connect to SNMP daemon if it is running. This elimintates the repeated (failed) connection attempts.
- [SNMP] Fix additional issue for SNMP support in routing daemons.
- [SNMP] Fix SNMP "refused smux peer" issue introduced by the SNMP support for routing daemons that was causing excessive logging.
- [Switch] Fix untagged packet handling issue on the ER-X platform introduced in beta1 that affects certain setups.
- Update bind9 to 1:9.8.4.dfsg.P1-6+nmu2+deb7u10: Fix CVE-2016-1285, CVE-2016-1286
- Update libssh2 to 1.4.2-1.1+deb7u2: Fix CVE-2016-0787
- Update openssl to 1.0.1e-2+deb7u21: Fix CVE-2016-0797, CVE-2016-0798, CVE-2016-0799, CVE-2016-0702, CVE-2016-0705 CVE-2016-2105, CVE-2016-2106, CVE-2016-2107, CVE-2016-2108, CVE-2016-2109
- Update openssh to 6.6p1-4~bpo70+1 (from wheezy-backports).
- Update perl to 5.14.2-21+deb7u3: Fix CVE-2016-2381
- Update squid3 to 3.4.8-6+deb8u2~bpo70+1: Fix CVE-2016-2571
- Update PHP to 7.0.7: Fix CVE-2015-8865, CVE-2016-4070, CVE-2016-4071, CVE-2016-4072, CVE-2016-4073, CVE-2016-4537, CVE-2016-4538, CVE-2016-4542, CVE-2016-4543, CVE-2016-4544, CVE-2016-3074, CVE-2016-4540, CVE-2016-4541, CVE-2016-4539, CVE-2016-3078, CVE-2013-7456, CVE-2016-5093
- Update mactelnet to 0.4.0-1 to fix segfault/crash.
- Update base-files to 7.1wheezy10 (sync to Debian 7.10)
- Update tzdata to 2016c-0+deb7u1 (sync to Debian 7.10)
- Update libidn to 1.25-2+deb7u1: Fix CVE-2015-2059
- Update eglibc to 2.13-38+deb7u11: Fix CVE-2016-1234, CVE-2016-3075, CVE-2016-3706
- Update expat to 2.1.0-1+deb7u4: Fix CVE-2016-0718, CVE-2016-0719, CVE-2012-6702, CVE-2016-5300
- Update libxml2 to 2.8.0+dfsg1-7+wheezy6: Fix CVE-2016-1762, CVE-2016-1834, CVE-2016-3705, CVE-2016-4483, CVE-2016-1840, CVE-2016-1838, CVE-2016-1839, CVE-2015-8806, CVE-2016-2073, CVE-2016-4449, CVE-2016-1837, CVE-2016-1835, CVE-2016-4447, CVE-2016-1833, CVE-2016-3627
- Update libtasn1-3 to 2.13-2+deb7u3: Fix CVE-2016-4008

:fill(white):strip_exif()/i/1396858301.jpeg?f=thumbmedium)
:fill(white):strip_exif()/i/1396858452.jpeg?f=thumbmedium)
:fill(white):strip_exif()/i/2001089077.jpeg?f=thumbmedium)
:strip_exif()/i/1396858687.png?f=thumbmedium)
:fill(white):strip_exif()/i/2001130391.jpeg?f=thumbmedium)
:fill(white):strip_exif()/i/2000774075.jpeg?f=thumbmedium)