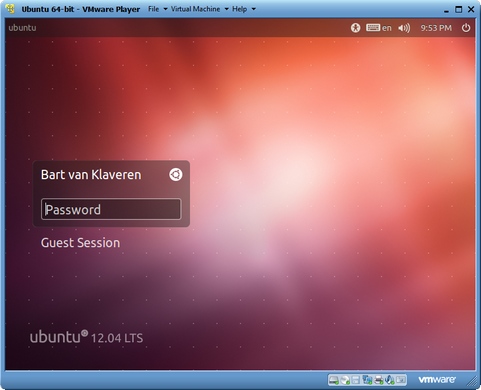
 VMware heeft versie 4.0.4 van Player uitgebracht. VMware Player is gratis software waarmee virtuele machines kunnen worden gedraaid die gemaakt zijn met andere VMware-producten, zoals Workstation, Server en ESX Server. Ook de virtual machines van Microsoft Virtual PC en Symantec LiveState Recovery-disks worden ondersteund. Daarnaast kunnen verschillende voorgeïnstalleerde virtual machines via deze pagina worden binnengehaald, zoals Debian, Ubuntu en Fedora. Versie 4.0 brengt diverse verbeteringen wat ondersteunde hardware betreft, maar daar staan wel verhoogde systeemeisen tegenover. In versie 4.0.4 zijn diverse bugfixes doorgevoerd en twee beveiligingsproblemen verholpen.
VMware heeft versie 4.0.4 van Player uitgebracht. VMware Player is gratis software waarmee virtuele machines kunnen worden gedraaid die gemaakt zijn met andere VMware-producten, zoals Workstation, Server en ESX Server. Ook de virtual machines van Microsoft Virtual PC en Symantec LiveState Recovery-disks worden ondersteund. Daarnaast kunnen verschillende voorgeïnstalleerde virtual machines via deze pagina worden binnengehaald, zoals Debian, Ubuntu en Fedora. Versie 4.0 brengt diverse verbeteringen wat ondersteunde hardware betreft, maar daar staan wel verhoogde systeemeisen tegenover. In versie 4.0.4 zijn diverse bugfixes doorgevoerd en twee beveiligingsproblemen verholpen.
General IssuesSecurity Issues
- Linux guests running the Linux kernel version 2.6.34 or later could not be pinged from the host via an IPv6 address.
- On rare occasions, Linux guests would suddenly fail to Autofit or enter Unity.
- Unity mode would exit if the title bar of an application contained certain non UTF-8 encoded extended ASCII characters.
- On Windows hosts, the VMware Workstation user interface sometimes became unresponsive when minimized from full-screen mode if the suggestion balloon was being displayed.
- On Windows hosts, the user interface sometimes became unresponsive if the application was rendered on an extended display that was abruptly disconnected.
VMware Security Advisory VMSA-2012-0011 documents workarounds and mitigation for these resolved issues.
- VMware host Checkpoint file memory corruption
Input data was not properly validated when loading Checkpoint files. This issue could have allowed an attacker with the ability to load a specially crafted Checkpoint file to execute arbitrary code on the host.
The Common Vulnerabilities and Exposures project (cve.mitre.org) has assigned the name CVE-2012-3288 to this issue.- VMware virtual machine remote device denial of service
A device (such as CD-ROM or keyboard) that is available to a virtual machine while physically connected to a system that does not run the virtual machine is referred to as a remote device. Traffic coming from remote virtual devices was incorrectly handled. This issue could have allowed an attacker who was capable of manipulating the traffic from a remote virtual device to crash the virtual machine.
The Common Vulnerabilities and Exposures project (cve.mitre.org) has assigned the name CVE-2012-3289 to this issue.

:fill(white):strip_exif()/i/2004010966.jpeg?f=thumbmedium)